Anthropic's Mythos AI finds software vulnerabilities far faster than humans can fix them, compressing discovery-to-exploit timelines dramatically.
Experts warn this speed advantage could empower attackers and outpace traditional cybersecurity defences.
The rapid discovery of flaws, including in major systems and browsers, is prompting urgent security responses worldwide.
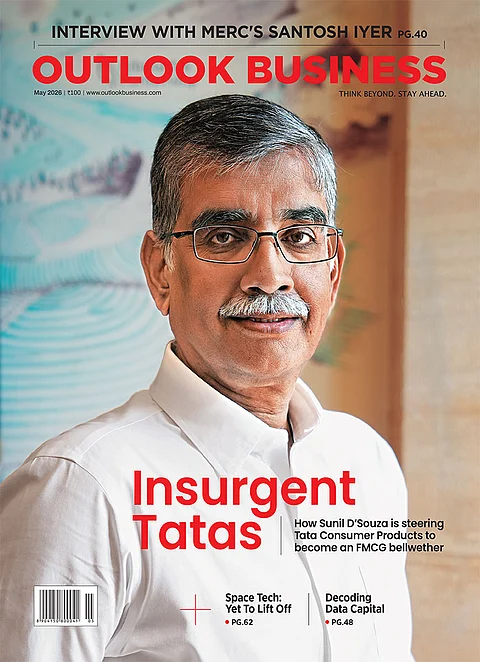
When Anthropic introduced its latest AI model, Claude Mythos Preview, the focus was on how powerful the technology had become.
But during the introduction, the company also did something unusual, it released a warning. Anthropic itself cautioned that Claude Mythos Preview does not just write better code, it finds the cracks in existing code with a speed and precision that no human security expert can match. And once it finds them, it can exploit them.
That discovery is now worrying cybersecurity experts, banks, regulators and technology companies. The concern is simple. The same AI tools that help developers write software faster may also help attackers break into systems faster.
The implications, security experts say, stretch far beyond Silicon Valley. From India's banking infrastructure to the safety of the UPI payments platform used by over 800 million people, the arrival of Mythos has set off alarm bells that are growing harder to ignore.
A Machine That Moves Faster Than Any Defence
In just seven weeks, the model identified over 2,000 previously unknown software vulnerabilities, flaws that human cybersecurity experts had missed for decades. It found weaknesses in every major operating system and web browser currently in use.
Ashish Tandon, Founder and CEO of Indusface, one of India's leading application security firms, says this is not an incremental improvement, it is a rupture. "Mythos didn't invent a new attack. It collapsed a timeline," he says. "The window between discovery and weaponisation had been narrowing for years. Now it's gone."
The consequences for organisations are severe. Tandon points to his company's own State of Application Security report, which found that 32% of high and critical vulnerabilities remain unaddressed even after 180 days. Meanwhile, AI-built applications face their first exploit attempt within just 18 days of deployment. "Defenders measure remediation in months. Attackers measure exploitation in weeks. Mythos widens that gap," he warns.
Anthropic itself has acknowledged the danger. The company stated that Mythos can complete cybersecurity tasks that, prior to April 2025, no AI model could complete at all, and warned that such capabilities could make cyberattacks faster, cheaper, and significantly more damaging, pushing them to or beyond human-level sophistication.
A Coalition Against the Storm
In direct response to the risks its own model revealed, Anthropic launched Project Glasswing, a cross-industry initiative to reinforce software security infrastructure before vulnerabilities can be weaponised at scale. The coalition includes some of the world's most powerful technology companies; Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorgan Chase, the Linux Foundation, Microsoft, NVIDIA, and Palo Alto Networks.
But the project's credibility took a hit almost immediately. Reports emerged that a small group of unauthorised users had already accessed Mythos. For Tandon, the breach exposed a fundamental flaw in the thinking behind controlled access programmes. "You can gate a model. You cannot gate a capability," he says.
His point is backed by research. A study by AISLE found that eight out of eight AI models tested, including one costing just eleven cents per million tokens, were able to replicate Mythos' core vulnerability-finding capability. The technology, in other words, is already commoditising. "Anthropic's access programme buys time, not safety," Tandon says. "The right threat model assumes attackers already have an equivalent capability."
Nilesh Bhojani, Chief Product and Technology Officer at data security firm Seclore, resonated with that point. "Controlled access programmes manage distribution, not motivation. Once a capability of this value exists, it is unrealistic to assume it will remain confined for long," he says. Bhojani points to the supply-chain dimension as particularly alarming, a single vulnerability in a widely used open-source component can cascade simultaneously across applications, vendors and data processors at a speed no human response team can match.
What This Means for Indian Banks
Nowhere is the risk more concentrated, or more consequential, than in India's financial system. The country's digital payments infrastructure, built around UPI and serving over 800 million users, sits on a technology layer that Mythos-class AI can scan and probe with ruthless efficiency.
Tandon identifies three specific vulnerabilities that make India's banking ecosystem uniquely exposed.
The first is an inventory gap. Legacy core banking systems cannot be patched quickly because uptime is non-negotiable for banks. Meanwhile, the modern API layers built on top of these systems grow faster than banks can track. "In our experience, financial services typically have 30-40% more APIs in production than their internal inventories reflect," Tandon says. "You cannot protect what you have not inventoried."
The second is a regulatory bind. The RBI Cyber Security Framework holds banks accountable for both patching vulnerabilities and maintaining uptime, two objectives that are increasingly in conflict. When a model like Mythos surfaces hundreds of vulnerabilities faster than teams can safely address them, it creates what Tandon describes as "timestamped evidence of known unaddressed risk", a compliance liability sitting on top of a security exposure.
The third, and perhaps most urgent, concerns UPI itself. "The highest-consequence risks are business logic vulnerabilities, API misconfigurations, and client-side script injection on payment pages," Tandon explains. PCI DSS 4.0, the latest global standard for payment security, now requires monitoring of third-party scripts on payment pages, a control the industry is still in the process of building. "The gap that matters most for UPI is not vulnerability discovery, AI-powered or otherwise, but protection on the business-logic and client-side surface where these attacks land," he says.
Is Regulatory Response Fast Enough?
Finance Minister Nirmala Sitharaman recently described Mythos as an "unprecedented" shift, directing the Indian Banks' Association (IBA) to establish a unified institutional mechanism for real-time threat intelligence. The government's broader strategy also includes setting up specialised AI War Rooms.
Bhojani acknowledges the intent is right, but argues the architecture is targeting the wrong moment. "The RBI and IBA measures are timely and directionally correct, but they address detection and coordination after exposure," he says. "The structural gap is earlier in the chain." Indian banks are actively piloting AI across credit, operations, and customer service right now, and most do not yet have governance frameworks that track where sensitive data flows once an AI system or third-party vendor touches it.
His prescription is direct, he says, "Restricting AI usage is not a workable answer—it pushes activity outside governed environments without reducing risk. Safe enablement means building the infrastructure to see where sensitive data exists, control how it moves across AI systems, and produce continuous auditability."
On the question of whether India should push for a multilateral regulatory framework, a Basel-style accord for frontier AI, Bhojani is supportive but realistic. "A multilateral framework is worth pursuing, but the Basel analogy only goes so far," he says. "Basel works because capital is quantifiable. AI risk is harder to standardise because the attack surface shifts with every model update." He further warns that institutions waiting for regulatory clarity before building governance architecture will find themselves behind. "The exposure is accumulating now."
New Rules of the Game
The arrival of Mythos has forced a fundamental rethink of how cybersecurity works. The old model—find a vulnerability, raise a ticket, ship a patch in days or weeks—is broken. Both Tandon and Bhojani converge on the same conclusion that the only viable response is machine-speed protection, not machine-speed patching.
"The new enterprise benchmark is 72 hours to neutralise exposure, not 180 days to ship a patch," says Tandon.
For India, a country that has built one of the world's most ambitious digital financial infrastructures, the stakes could not be higher. The AI that helps a bank spot fraud faster can also help a criminal break in faster. That is the uncomfortable truth sitting at the heart of the Mythos debate.